Shannan Travel Guide
Shannan Facts
Chinese Name: 山南 (shān nán)
Population: 375,300
Area: 79,300 square kilometers (30,618 square miles)
Location: in the south of Tibet, southwest China
Administrative Division: 1 districts (Nedong); 11 counties (Dranang, Gonggar, Sangri, Chonggye, Qusum, Comai, Lhuntse, Gyatsa, Lhuntse, Cona, Nagarze)
Area Code: 0893
Zip Code: 856000
GDP (2018): CNY 16.432 billion (USD 2.483 billion)
Nationalities: Tibetan, Han, Hui
The Birthplace of Tibetan Culture & Best Place to See Tibetan Customs
Lying in southern Tibet, Shannan also known as Lhoka is bordered by Lhasa to the north and in the neighborhood of Shigatse and Nyingchi to the west and east. Its south boundary is with India and Bhutan. This city is only 150 kilometers (93 miles) from Lhasa. Shannan is the birthplace of the Tibetan people and Tibetan culture. It boasts many “firsts” in Tibetan history, including the first palace, Yongbulakang Palace; the first Buddha hall, Trandruk Monastery; and the first monastery, Sangye Monastery.
Besides, Shannan is covered with the most representative scenery in Tibet including snow mountains, lakes, hot springs, canyons, grasslands, high mountains and virgin forests. Yamzho Yumco Lake, one of the three holy lakes in Tibet, is regarded as "turquoise earrings of the goddesses". The blue lake water changes with the light. There is a road along the lake not far from the Snow Mountain. Walking or camping by the lake is the best way to appreciate Yamzho Yumco Lake.
|
|
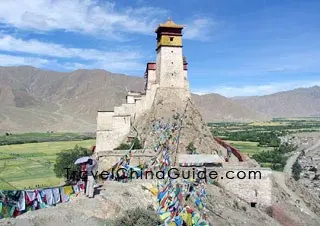
![]() Yumbu Lhakhang Palace: Located 5 kilometers (3 miles) southeast of Nedong County, there is a building similar in shape to a blockhouse standing on top of a hill. That is the Yumbu Lhakhang Palace, the oldest palace on that high land built over two thousand years ago for the first Tsampo (king) of the Tubo tribe, although through extension, the palace gradually became a Buddhist monastery.
Yumbu Lhakhang Palace: Located 5 kilometers (3 miles) southeast of Nedong County, there is a building similar in shape to a blockhouse standing on top of a hill. That is the Yumbu Lhakhang Palace, the oldest palace on that high land built over two thousand years ago for the first Tsampo (king) of the Tubo tribe, although through extension, the palace gradually became a Buddhist monastery. ![]() Trandruk Monastery: On the way back to Nedong, a visitor can stop to make a trip to the famous monastery, Trandruk Temple, which is at the south foot of the Gungbort Mountain about 2 kilometers (1.2 miles) south of the county seat. The Pearl Thangka Painting preserved in the temple is a precious treasure.
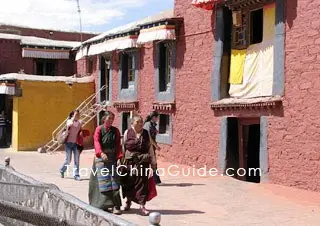
Trandruk Monastery: On the way back to Nedong, a visitor can stop to make a trip to the famous monastery, Trandruk Temple, which is at the south foot of the Gungbort Mountain about 2 kilometers (1.2 miles) south of the county seat. The Pearl Thangka Painting preserved in the temple is a precious treasure. ![]() Samye Monastery: Along the Yarlung Zangbo River from Tsedang Town of Nedong County to Dranang County, the Samye Monastery is situated on the north bank of the river. Visitors can take powerboat or sheepskin draft to cross the river. The monastery was first built in 762 combining buildings of Tibetan, Han and ancient Indian styles. In addition, it is the first temple complete with all the three treasures of Buddhism: hierarchy, doctrine and monk, regarded as the headstream of Tibetan Buddhism.
Samye Monastery: Along the Yarlung Zangbo River from Tsedang Town of Nedong County to Dranang County, the Samye Monastery is situated on the north bank of the river. Visitors can take powerboat or sheepskin draft to cross the river. The monastery was first built in 762 combining buildings of Tibetan, Han and ancient Indian styles. In addition, it is the first temple complete with all the three treasures of Buddhism: hierarchy, doctrine and monk, regarded as the headstream of Tibetan Buddhism.
![]() Other Scenic Spots: Tombs of Tibetan Kings, Lhamoi Lhatso Lake, Yamzho Yumco Lake, Samding Monastery, Mindroiling Monastery, Lhamo Latso
Other Scenic Spots: Tombs of Tibetan Kings, Lhamoi Lhatso Lake, Yamzho Yumco Lake, Samding Monastery, Mindroiling Monastery, Lhamo Latso
|
|
How to Get to Shannan
The regular route to Shannan is getting to Lhasa by air and taking buses from Lhasa Bus Station at 1, Minzu Lu, Chengguan District to the capital of the region, Tsedang Town. The distance between them is about 190 kilometers (118 miles). The address of Shannan Bus Station is 21, Gesang Lu, Tsedang Town, Nedong County.
In Quxu County of Lhasa, Tsedang Town, Chonggye County, Gonggar County and Nanggarze County lodgings can be found while traveling to Shannan.
Weather
Enjoying a semi-dry continental plateau climate, the region has four vague seasons with an annual average temperature of 5-8℃ (41-46.4℉). During the rainy season from June to September, rain usually falls at night which is a salient characteristic of the weather in this plateau area. In consideration of the road and traffic conditions, the months April to October are the best time to pay a visit.
Shannan Travel Tips
![]() History: Shannan is located in the catchment area of the Yapan River, hence its old name of Yapan. The region is the headstream of the Tibetan nation and culture. About forty or fifty thousand years ago, the first ancestors of the Tibetan people moved there. During the early years of the 2nd Century BC, the first Tibetan Kingdom got its start. A legend passing around in this region is about monkeys changing to human beings. The first farmland and village, the first king and palace as well as the first monastery of the high land were also all born here.
History: Shannan is located in the catchment area of the Yapan River, hence its old name of Yapan. The region is the headstream of the Tibetan nation and culture. About forty or fifty thousand years ago, the first ancestors of the Tibetan people moved there. During the early years of the 2nd Century BC, the first Tibetan Kingdom got its start. A legend passing around in this region is about monkeys changing to human beings. The first farmland and village, the first king and palace as well as the first monastery of the high land were also all born here.
 |
| Shannan Region |
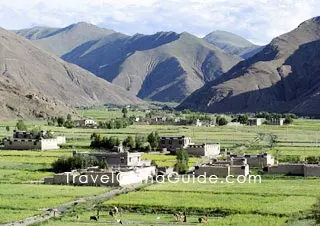
![]() Physical Features: The region lies in the south of the Kangdese Mountains and Mt. Nyainqentanglha on the middle and lower reaches of the Yarlung Zangbo River. Its southern area is higher than the north and the west is higher than the east. There are lofty mountains standing and lakes and rivers crisscrossing in the south and west region of Shannan. The whole region is situated in the valley zone between the Kangdese Mountains and the Himalayas.
Physical Features: The region lies in the south of the Kangdese Mountains and Mt. Nyainqentanglha on the middle and lower reaches of the Yarlung Zangbo River. Its southern area is higher than the north and the west is higher than the east. There are lofty mountains standing and lakes and rivers crisscrossing in the south and west region of Shannan. The whole region is situated in the valley zone between the Kangdese Mountains and the Himalayas. ![]() Local Highlights: As mentioned, Shannan is the cradle of the Tibetan nation and culture, where the first farmland, village, palace, temple, and sutra were given birth. In fact, it is also the birthplace of Tibetan Opera. Festivals and customs, garments and ornaments there are greatly affected by the opera. Different masks represent different characters. The red is for the king, the green for the queen, the yellow for the Living Buddha and god, while the mask, with half in black and half in white, is for the informer or witch
Local Highlights: As mentioned, Shannan is the cradle of the Tibetan nation and culture, where the first farmland, village, palace, temple, and sutra were given birth. In fact, it is also the birthplace of Tibetan Opera. Festivals and customs, garments and ornaments there are greatly affected by the opera. Different masks represent different characters. The red is for the king, the green for the queen, the yellow for the Living Buddha and god, while the mask, with half in black and half in white, is for the informer or witch
![]() Special Local Products: Tibetan incense, Thangka (religious painting), golden, silver and jade ornaments, hanging carpet, Tibetan Opera mask, Gyatsa walnut
Special Local Products: Tibetan incense, Thangka (religious painting), golden, silver and jade ornaments, hanging carpet, Tibetan Opera mask, Gyatsa walnut